Dedicated specialist facilities where students have access to commercial grade networking hardware and software, virtual computing environments, forensic tools and more.
Networks & Cyber Security has a home in four specialist teaching areas within the Mellor building, two dedicated network labs and two forensic labs which can also operate as one large teaching space. These areas are supported by two server/equipment rooms.
As well as access to the corporate network, the machines in these rooms all have access to an internal isolated network which allows the building and configuration of test network topologies, investigation and troubleshooting of networks, simulated cyber attacks and access to virtual images used as attack targets.
Machines in these labs all host specialist Virtual Machines, Microsoft and Linux, configured with specialist software and applications such as Packet Tracer, Wireshark, EnCase and XRY.
Other virtual machines installed;
- Kali Linux virtual machine which provides information security training and penetration testing.
- CyberOps virtual machine which simulates an environment to implement and analyse security threats.
- Security Onion virtual machine for threat hunting, enterprise security monitoring and log management.
- Metasploitable virtual machine to provide a vulnerable target for attack simulation.
The Network labs are connected by a CAB room which contains 400+ industry standard network devices, mostly Cisco and Cisco Meraki switches, routers, firewalls, wireless LAN controllers and network traffic generators. These are housed in racks and constantly available for use by students. They can be wired to create a desired topology and configured from any machine in the lab.
The Cyber labs also host similar virtual machines hosting specialist software with access to powerful forensic tools used in the recovery of data and criminal investigations. There are also hardware kits to support the software which enables the recovery of data from a wide range of devices such as PCs, phones, mobile devices, watches and Sat Nav units.
Students can build virtual computing environments to suit research and project work on our dedicated server provision. This is housed within our own data centre which also hosts our internal network. We have an array of Dell and HP servers and also two Passware distributed password recovery devices.
Equipment
-
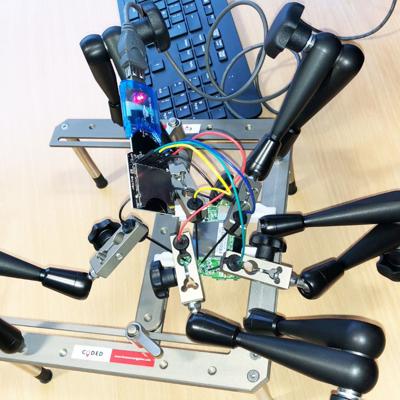
CODED – Chip on data extraction device.
-
XRY Mobile Forensics Extraction Kit. × 5
-
Cellebrite Mobile Forensics Extraction Kit. × 5
-
Cisco Switches (multiple)
-
Cisco Routers (multiple)
-
Cisco ASA Firewalls × 14
-
Cisco Wireless LAN Controllers × 6
-
East Coast Traffic Generator

Rack containing live kit.
Retrieving data from Sat Nav board.
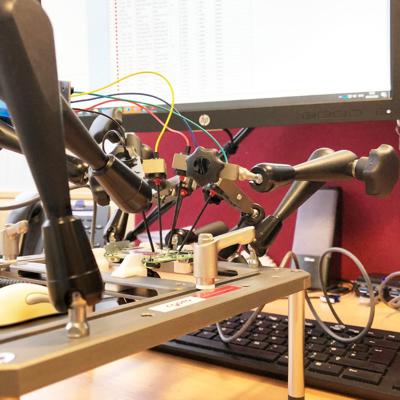
Retrieving data from Sat Nav board.